First off, props to you for caring about your online security and privacy enough to use a VPN to prevent you from data breaches and hacks. It’s the frontline of internet defense these days.
However, security has no upper limit. For example, what should you do to prevent disease or a virus like the flu? Some indicate doing more exercise. Some say exercise alone isn’t enough and keeping a balanced diet is also needed. Some say exercise and diet aren’t enough and a good mood is what’s called for. The more people you ask, the more answers you get.
It’s the same with the case of Internet security. Different people all swear by different measures, and yet every year millions of computers are left exposed as gaps in the armor are discovered. One of the big debates these days is whether it is better to use a centralized VPN or a decentralized VPN. Well, both are used to cater to different security requirements and levels of protection. We’ll be running through each and letting you know what to choose for peace of mind. If you want the short answer, it’s a decentralized VPN like BitVPN.
Do You Know Whether Your Installed VPN is Working Or Not?
As most providers claim, most VPNs can do the following:
- Hide Your IP Address
- Bypass Internet Censorship
- Prevent Data Breaches
- Build Encrypted Tunnels for Data.
However, when trying to finally protect your online security and privacy, how do you determine that the above functions are enough? Can your device’s installed VPN do more? Apart from bypassing local restrictions, it’s difficult to discover the other functions. Is my IP address really unknown by my Internet Service Provider, also called ISP? Can I really browse anonymously? Are my online activities really safe? If you’ve got any doubts about those things, then read on – you might well be right.
Using a fake, disreputable, or simply the wrong type of VPN can be more dangerous than using none at all. All your online data may be easily obtained or sold without your awareness. Worse still, your VPN providers have the overall opportunity to abuse your online data.
How does a Centralized VPN Protect Your Online Security and Privacy?
Check the details of your VPN. Maybe the term ‘centralized VPN’ is a new one for you, but that’s what you’re most probably using. It is also known commonly as a ‘traditional VPN’ or directly ‘VPN’. Basically, a centralized VPN connects you to the Internet much like using a proxy to hide your identity. The connection between you and the proxy is encrypted to stop others from snooping on you. Without this traditional type of VPN, as you connect to the Internet through public WiFi or your ISP, all your online activities are easily discoverable.
In terms of centralized VPNs, there are two huge disadvantages:
Closed Source Code
The closed source code feature of centralized VPNs stops others from having knowledge of the protection processes and coding used by the VPN provider. Unfortunately, the VPN provider isn’t excluded. Only the VPN providers have the opportunity to see and process the data, so you have to trust it isn’t open to backdoor entries or attacks the company may not have foreseen. But truthfully, they can be hacked. And then you’ll be trapped in trouble.
It’s tremendously shocking and sad to hear that 20 million VPN users’ data are leaked through using a VPN, but it’s true. It’s suggested you check the list of insecure VPNs so as to stay away from more traps.
Centralization
Centralization refers to the fact that as you get connected to the VPN, all the traffic will be transmitted through centralized VPN servers. That means all the information is accumulated and stored in the provider’s servers… which isn’t great.
Yes, most VPN providers promise not to log data. But that’s a myth. And there’s no way to prove that. All VPN providers have privacy policies but the real extent to which they conform to them is unknown. And what often happens is that they sell your data for profit – that’s especially often the case with these ‘free’ VPNs.

What is a Decentralized VPN?
Now you know the disadvantages of centralized VPN, it’s not difficult to imagine where a decentralized VPN stands. The decentralized structure prevents any type of logging from being possible. It means your traffic is distributed to the whole network and there’s no single node that can fully process or know who you are and what you’re doing. That means it’s not up to a flimsy privacy policy to keep your data safe.
Let’s dig into the question, what is a decentralized VPN, by studying how it can do the above.
Open Source
The open-source feature allows any developer to check the codes to find suspicious elements. Moreover, any weak links within the network can be found and brought to the developer’s attention.
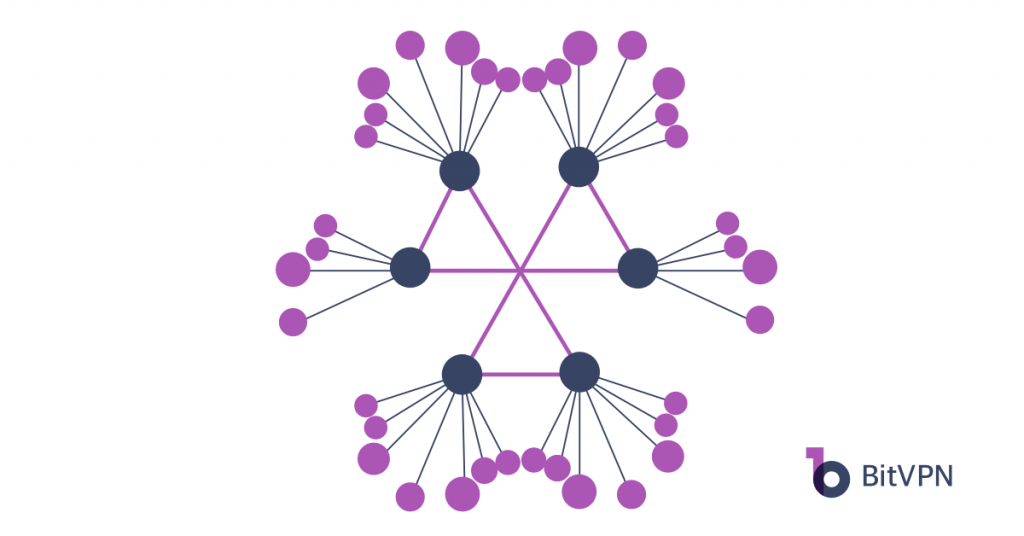
Peer-to-peer Mesh Network
A peer-to-peer mesh network – or a p2p mesh network – is created where different network layers are concerned. As a type of topology structure, mesh networking is used to organize nodes into a network where data can be transmitted between nodes without physical contact. P2P refers to the fact that nodes can directly communicate with each other for information exchange.
Blockchain Technology
Blockchain technology is one of the most popular technologies in recent years. The block and chain in blockchain technology are actually digital bits of information stored in public databases. Blocks store information concerning trade, such as trading date, time, and amount. Apart from that, blocks also store the information concerning participator – not the real name, but a digital signature will be recorded. Blocks are identified by unique codes that play a role as names.
In a word, a blockchain-based decentralized VPN doesn’t rely on a single central server. Since it doesn’t have single permission, the system will be self-justifying and more secure. To log the data on a blockchain represents the internal value of decentralization. A decentralized VPN compiles much traffic from numerous computers and the communication is equivalently used. It also means that each PC can play a role as a server. So when a hacker wants to compromise the VPN server, it is impossible unless all the participating PCs are attacked.
Therefore, a decentralized VPN does a better job of protecting your online security and privacy than a centralized VPN.
Summary Comparison between Centralized and Decentralized VPN
To teach you the difference between a centralized VPN and a decentralized VPN, a summarized table is shown below.
| FEATURES | CENTRALIZED VPN | DECENTRALIZED VPN |
| RESTRICTION BREAKING | √ | √ |
| ANONYMOUS BROWSING | unknown | Definitely yes |
| IP ADDRESS | unknown | Definitely yes |
| ENCRYPTED TUNNEL | unknown | Definitely yes |
| BLOCKCHAIN BASED | × | √ |
| P2P MESH NETWORK | × | √ |
| UNSTOPPABLE | × | √ |
| SECURITY | Low | High |
| COST | Low | Relatively High |
Therefore, to better your online security and privacy, a decentralized VPN is a better solution.
You May Also Like:
- How to Tell if Someone is Spying on My Phone and How to Stop That
- Ask Your Employees These Questions to Easily Test Their Cybersecurity Awareness
- What’s Computer Hacking and How to Prevent It
- What is Ransomware? Everything You Should Know About Top 1 Possible Cyberattack in 2021
- Affected by Facebook Leak? How to Stay More Private on Social Media